The success of mobile apps has soared in recent years, largely as a result of the advent of the smartphone and the equally meteoric rise of the iPhone. The phrase “there’s an app for that” has become a common phrase in our everyday vocabulary and is today more likely to be said than “there’s a website that can…” and this is reinforced by the fact that mobile apps now have penetration rates of more than 50% in many developed markets.
Millions of apps have been downloaded from Apple’s App Store and the Android Market, with mobile apps now overtaking web browsing as consumers’ favourite mobile past time. However success always attracts those looking to making a quick buck on the back of it, often using some form of fraudulent activity and the world of mobile applications is no exception. Amethon, who offer a range of services to measure mobile analytics, have recently published a report, detailing the threats associated with mobile applications.
Amethon’s research reveals a number of apps that pose a threat and the most worrying fact is that many of these apps are used by millions of people every day, especially when we consider that the average user now has 41 apps on their phone. Before we name and shame these apps, it is important to understand what constitutes as a threat and how this malicious behaviour occurs via mobile apps.
Malicious apps are those that send high cost texts from a users phone, cause a charge for free apps and steal sensitive information, whereas the largest threat comes from apps that use a high amount of data and place a strain on mobile networks. These apps effectively waste mobile data and this leads to higher costs for both networks and individual users, with those causing continuous data transfers, without users realising, leading to a huge amount of mobile data being used. According to Amethon’s research, T Mobile have seen signalling rise by more than 1000% as a result of malicious apps and O2 have complained of severe network congestion, preventing the streaming of live data.
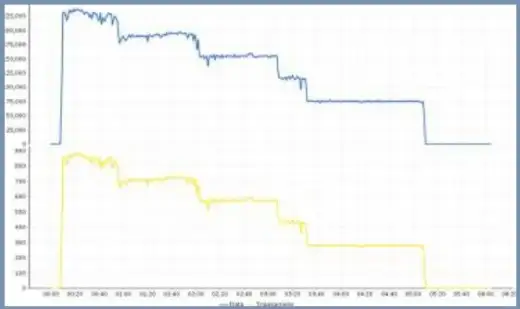
So the time has come to look at which apps pose the greatest threat and the result will surprise you, as the Facebook app for iPhone is one of the biggest culprits. This is because it continually sends and receives mobile data, for hours on end and the graph below depicts the amount of information sent and received by the iPhone Facebook app during a 5 hour period. Across these 5 hours the apps caused a staggering 170,000 data transactions and this led to the unnecessary consumption of 50mb of data. Other apps that you may use everyday, which lead to similar data usage, include Yahoo’s Android Messenger and even a typical Android media player.
These apps lead to higher mobile bills for consumers and in turn cause dissatisfaction with their network provider, which causes them to incur further costs in terms of customer service. So the question is how you can identify and nullify the threat of these potentially harmful apps?
Mobile networks need to make a greater effort to identify such apps before they lead to data outages and there are a number of tools available to make this possible, with any information gained being passed onto customers and increasing awareness. Similarly there are tools that prevent any data usage from defective apps and it is advisable to use these and finally it may be a good idea to contact the developers of the app, who may wish to make changes in light your advice.